Zero-Day Exploits: How Governments Buy the Keys to Your iPhone
how the FBI paid $1M for a zero-day bug to hack an iPhone after Apple refused. Learn about the shadowy gray market, Project Raven, and what this means for your digital privacy.
The Digital Lockpick: When Governments Pay Millions to Bypass Your Phone’s Security
Imagine this: you’re sitting at home, scrolling through your phone, completely unaware that a government agency halfway across the world has just unlocked your device without your knowledge—or your consent. No password guess, no physical access, no warning. Just a silent, invisible breach.
This isn’t a scene from a spy thriller. It’s the reality of modern cybersecurity, where powerful governments like the U.S. and the UAE operate in a shadowy “gray market” to buy digital weapons known as zero-day exploits. These are hidden flaws in software—like iOS or Android—that developers don’t even know exist… until someone pays millions to use them against you.
In this deep dive, we’ll uncover:
The true story behind the FBI’s $1 million iPhone hack.
How the San Bernardino case changed the game for digital privacy.
The chilling tale of Project Raven: UAE’s cyber mercenaries who hacked iPhones with a single text message.
Why the zero-day market is a ticking time bomb for global security.
And what you can do to protect yourself in an era where your phone is never truly private.
Let’s pull back the curtain on the secret economy where your personal data is the ultimate commodity.
The San Bernardino Standoff: Apple vs. The FBI
It all began in December 2015. After a terrorist attack in San Bernardino, California, left 14 people dead, investigators turned their attention to the iPhone 5c belonging to one of the shooters. The phone was locked with a passcode, and Apple’s built-in security features were designed to erase all data after ten failed attempts—a safeguard meant to protect users from brute-force attacks.
The FBI wanted Apple to create a custom version of iOS that would disable this auto-erase function, effectively creating a backdoor into the device. Apple refused, arguing that building such a tool would compromise the security of every iPhone user and set a dangerous precedent for government overreach.
As our video highlights, Apple famously responded with the words: “We refuse.” The company stood firm, citing user privacy and the integrity of its encryption. But the FBI didn’t back down. Instead, they turned to the underground.
“The FBI had to go to the gray market to hack into it.”
They found a third-party contractor willing to sell them a zero-day exploit—a previously unknown vulnerability in iOS—for a reported $1 million. Within weeks, the FBI gained access to the phone, and the standoff ended… but not without exposing a terrifying truth: if a government wants into your device, they can buy the key.
What Is a Zero-Day Exploit? (And Why It’s Worth Millions)
A zero-day exploit is a software vulnerability that the vendor (like Apple or Google) doesn’t yet know about—and therefore hasn’t patched. The term “zero-day” refers to the fact that developers have “zero days” to fix the flaw before it’s actively being used in an attack.
These exploits are incredibly valuable because they offer guaranteed access to systems that are otherwise secure. Once discovered, they can be sold to:
Government agencies (FBI, NSA, CIA, etc.)
Intelligence contractors
Private corporations
Cybercriminals
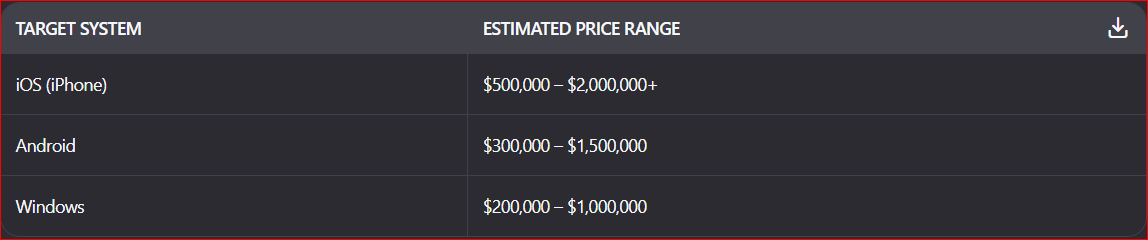
The market operates in secrecy, often through brokers who connect hackers with buyers. Prices vary based on the target system and the exploit’s capabilities:
Why is it so expensive? Because once an exploit is used, the vendor patches it—and the value disappears. So agencies pay top dollar to keep these tools secret for as long as possible.
Project Raven: The UAE’s Secret Cyber Army
If the FBI’s iPhone hack was shocking, the UAE’s Project Raven was downright dystopian.
According to investigations by The New York Times and The Guardian, the United Arab Emirates hired former U.S. intelligence operatives, including ex-National Security Agency (NSA) and Central Intelligence Agency (CIA) officers, to build a sophisticated cyber-espionage unit called Project Raven.
Their mission? To monitor dissidents, journalists, political rivals, and even foreign diplomats—both inside and outside the UAE.
One of their most potent tools was called Karma. This software allowed operatives to hack into iPhones remotely—without any interaction from the target. All it took was sending a malicious message or link. If the victim opened it—even just viewed a picture—their phone could be compromised.
“Raven operatives could access information on a target’s iPhone without the target having to click or do anything.”
Karma gave the UAE unprecedented access to emails, messages, location data, and even microphones and cameras. It was a digital surveillance weapon, bought and deployed with impunity.
Project Raven exposed a disturbing trend: nations without large indigenous cyber capabilities can simply buy them on the open market. Private companies become state-sponsored hackers. Personal devices become instruments of state control.
The Gray Market: Where Hackers Become Mercenaries
The video’s depiction of hooded figures and shadowy dealings isn’t hyperbole—it’s accurate. The gray market for zero-day exploits is a thriving, multi-million-dollar industry where ethical boundaries blur.
Security researchers discover critical flaws and then choose between:
Reporting them to the vendor (often for a modest bounty or public recognition).
Selling them to a broker (for hundreds of thousands—or millions—of dollars).
The financial incentive is enormous. A single zero-day for a popular mobile OS can fetch upwards of $1 million. This creates a perverse ecosystem where keeping vulnerabilities secret becomes more profitable than fixing them.
And here’s the kicker: when a government buys a zero-day, they rarely disclose it to the vendor. That means millions of users remain vulnerable until the flaw is eventually discovered and patched—often only after it has been used for espionage or surveillance.
The Ethical Dilemma: National Security vs. Digital Privacy
This is the core tension of our digital age.
On one hand, zero-day exploits can be vital tools for law enforcement and national security. They help prevent terrorist attacks, catch child predators, and disrupt criminal networks. In the San Bernardino case, the FBI argued that accessing the shooter’s phone was essential to understanding his motives and preventing future attacks.
On the other hand, these tools represent a fundamental threat to civil liberties. When a government can hack into your phone without your knowledge or consent, the very notion of personal privacy is eroded. As Edward Snowden warned, “Arguing that you don’t care about the right to privacy because you have nothing to hide is no different than saying you don’t care about free speech because you have nothing to say.”
The challenge for society is to find a way to regulate this market without stifling innovation or compromising security. Until then, every smartphone user should be aware that their device may be more vulnerable than they think—and that the keys to their digital life might be sitting in a government vault, purchased for a million dollars on the dark web.
What Can You Do to Protect Yourself?
While you can’t stop a nation-state from targeting you with a zero-day exploit, there are steps you can take to minimize your risk:
✅ Keep Your Software Updated: Patching fixes known vulnerabilities. Turn on automatic updates for your phone, apps, and operating system.
✅ Use Strong, Unique Passwords: Combine letters, numbers, and symbols. Never reuse passwords across accounts.
✅ Enable Two-Factor Authentication (2FA): Adds an extra layer of security beyond just a password.
✅ Be Wary of Suspicious Links: Don’t click on links or download attachments from unknown senders—even if they look legitimate.
✅ Use Encrypted Messaging Apps: Signal and WhatsApp (with end-to-end encryption enabled) offer stronger privacy protections than SMS or standard email.
✅ Consider a VPN: Encrypts your internet traffic, making it harder for attackers to intercept your data.
✅ Review App Permissions: Regularly check which apps have access to your camera, microphone, location, and contacts—and revoke unnecessary permissions.
Conclusion: Your Phone Isn’t as Secure as You Think
The story of the FBI’s $1 million iPhone hack, the shadowy gray market, and Project Raven’s remote hacking capabilities reveals a sobering truth: in today’s world, your digital privacy is not guaranteed. It’s a privilege that can be bought, sold, and exploited by those with enough money and power.
Governments will continue to seek out zero-day exploits to serve their interests—whether noble or nefarious. And as long as there’s demand, there will be supply.
But awareness is the first step toward protection. By understanding how these exploits work, who uses them, and what you can do to defend yourself, you reclaim a measure of control over your digital life.
So next time you pick up your phone, remember: it’s not just a device. It’s a gateway—and someone, somewhere, might already have the key.
Want to stay ahead of the curve in digital security?
👉 Subscribe to our newsletter for weekly tips on protecting your data.
👉 Share this article with friends who need to know the truth about zero-day exploits.
External Links:
Darknet Diaries: Episode 82 - Master of PWN



This article comes at the perfect time, because I was just thinking about how important data privacy is after my pilates class, and you totally hit the nail on the head about how terrifying it is that governments can just buy zero-days like it's nothing.